Secure process for destroying data and electronic devices before selling them.
Technological advancements, increased connectivity, and the rise of the Internet of Things, businesses around the globe are collecting and storing ever-growing amounts of data. As such, secure data storage is a critical resource, one that needs to be effectively managed to benefit the organization and protect its employees and customers from data breaches.
As there are many devices that can store data, if there is not a secure process for destroying data and electronic devices before selling or donating, it may be recovered by malicious.
Devices list in this recommendation includes computers, smartphones, tablets, and digital devices that can record data.
Data destruction process recommendations as follows:
- Back up important data from the device. To prevent data loss Including to determine what information this malicious device may recover if it has not been destroyed by appropriate methods.
- Delete data in the device If it is a computer, use secure erase tools or disk wiping. If it is a smartphone or tablet Digital camera, music player Game console or office equipment such as printers, fax machines, clear data, and then remove the SIM card, hard disk, or memory card from the machine (if possible).
- To ensure that the malicious person will Unable to recover important data from the device. May use the way to overwrite the media by zero fill ( overwrite all sectors with 0 )
- If any equipment has very important information and don’t want others to continue using that device, the whole machine or important parts should be destroyed so that they can no longer be used, such as smashing or burning. Destruction may vary by device, for example Magnetic disk disks may Must use a magnetic field shredder For CDs, it may be necessary to use grinding and breaking methods.
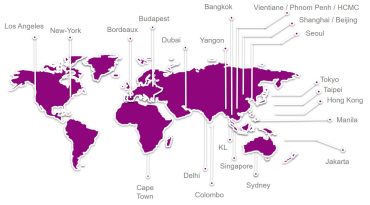
Asia Data Destruction very pleased and proud to offer the best Data Destruction Services.
We can help you to destroy Electronic devices properly and comply to the Personal Data Protection Act A.C 2563 correctly.


 ไทย
ไทย 日本語
日本語 Tiếng Việt
Tiếng Việt ភាសាខ្មែរ
ភាសាខ្មែរ